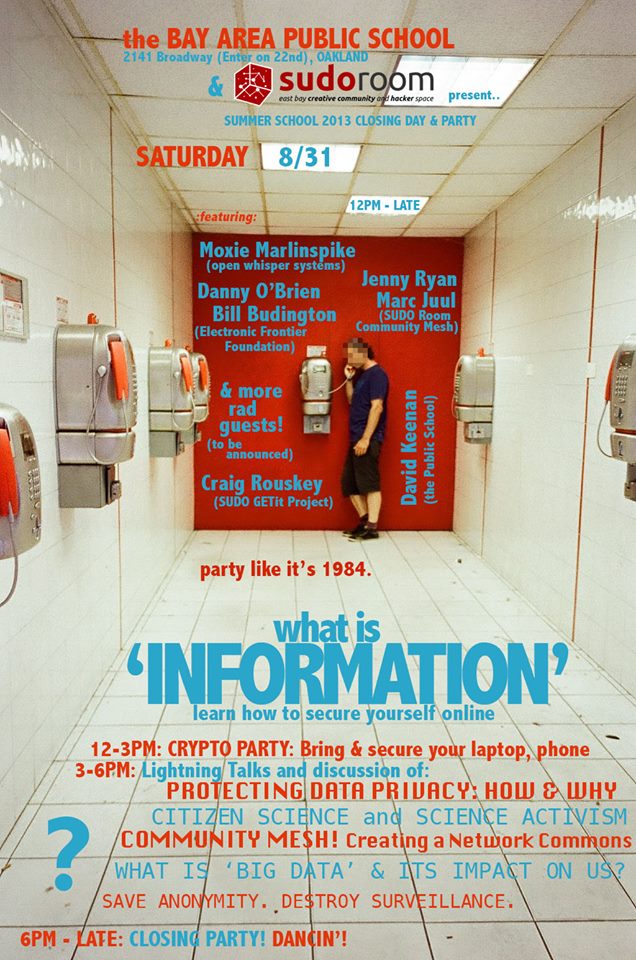
Cryptoparty
Every Third Sunday of the month from 2-5pm, Sudo Room hosts an afternoon of co-learning and teaching about digital security. The driving motivation of our cryptoparties is to learn about end-user security in a fun, welcoming and inclusive environment. Popular topics include: why digital security is important; strategies for activists and journalists; encrypted email; encrypted text messaging; encrypted phone calls; encrypting your hard drive; off-the-record instant messaging; secure web browsing; mesh networks; and presentations on newer projects. All skill levels welcome - bring your phone and/or laptop!

Archive
Ways To Volunteer For Non Coders
Translation Efforts:
- https://www.transifex.com/projects/p/Cryptocat/
- https://www.torproject.org/getinvolved/translation-overview.html.en
- https://tails.boum.org/contribute/how/translate/
- https://www.transifex.com/projects/p/torproject/resources/
Art:
- https://www.torproject.org/getinvolved/volunteer.html.en
- https://tails.boum.org/contribute/how/graphics/
Writing (documentation + press releases):
General Resources
- https://www.cryptoparty.in/brief
- https://securityinabox.org/en
- https://www.cryptoparty.in/documentation/handbook
- http://prxbx.com/email/
- http://tacticaltech.org
- http://prismbreak.com
Recommended Software
Warning: This table is intended as a starting point for new users. Web-based solutions, iOS devices, Pidgin, CryptoCat, and ChatSecure all have known flaws or associated risks that need to be considered.
| Android | iOS | Windows | OS X | Linux | Cross-platform or Web | |
|---|---|---|---|---|---|---|
| K9 | ?? | Thunderbird+Enigmail | GPGSuite Thunderbird, Enigmail | Thunderbird, Enigmail | riseup webmail | |
| Chat | GibberBot, TextSecure (sms) | TextSecure (sms) | ChatSecure | Pidgin, Adium | Pidgin | CryptoCat |
| Network Anonymity | Orbot, OrWeb | Tor | Tor | Onion Browser | Tor | Tor |
| Disk Encryption | Available in 4.0+ | ?? | TrueCrypt | Available in 10.7+ | LUKS | SecureDrop, Tahoe LAFS |
| Password Management | KeePassX, FreeOTP | FreeOTP, KeePassX | KeePassX | KeePassX | KeePassX | KeePassX |
Other Web Resources
- Surveillance Self-Defense
- EFF know your rights
- Liberation Tech Mailing-list
- Tent.io An interesting federated social identity network project
- Mozilla Security notes
- Which Countries Actively Suppress Internet Freedom?
- Alice and Bob in Cipherspace - Fully Homomorphic Encryption
Videos
- Diffie-Hellman Key Exchange
- How Tor Works
- Udacity: Applied Cryptography (cs387)
- khan academy: Journey into Cryptography
- Anti-Rep workshop (1/2) - Jacob Applebaum
- Anti-Rep workshop (2/2) - Jacob Applebaum
- What Happened to the Crypto Dream?
Books
- The code breakers - david kahn
- crypto - steven levy
- the code book - simon singh
- The Cuckoo's Egg - clifford stoll (fiction)
Online Courses
Hosting A Cryptoparty
- Cryptoparties are best when some planning takes place before. Hold a planning meeting 1-2 weeks before the event and ping the mailing list to recruit folks who've expressed interest in helping out.
- There are handouts linked to above that can be printed out at sudo - they generally live in a clear document holder / trapper keeper labelled 'Cryptoparty' located in a crate of other trapper keepers on the middle shelf between the workshop and the bike station in sudo.
- Try to reach out to communities that should be using crypto and are generally not connected to the sudo room social network. Activists, journalists, immigrants + expats, POC, etc; Consider hosting the cryptoparty in an entirely different location.
- At least a week before the cryptoparty, get the word out:
- Tweet/FB posts via Sudo Room's accounts (ask Jenny for info)
- Send an announcement to the following mailing lists:
- Come half an hour to an hour earlier to set up:
- Put the sudo room sandwich board out
- Tape up some signage on the doors if so inclined (there are some paper signs in the clear trapper keeper)
- Find a good spot for your expected # of attendees. Check with Public School; often we have split up into several working groups using different areas of the common space, sudo room proper, and the public school room.
- Starting the cryptoparty:
- Take notes on the wiki - set up a separate wiki page for that month's event [eg; /wiki/Cryptoparty/YEAR/MONTHNAME
- Allow 15-30 minutes to get to a good group size to start
- Go around the room and ask folks to introduce themselves, their level of skill w/ crypto, what they're interested in discussing or working on that afternoon.
- Create an agenda ad-hoc and split the group as needed (pairs work great for things like helping someone set up disk encryption)
- Have fun! Encourage wide-ranging discussion but step in if things start to get to technical. Keep focus on those who are newer to the topic and have specific things they want to accomplish.
Flyers and Handouts
- Tools for Protecting Against Online Snooping
- Security Overview (work in progress, don't print)
- Minimum Security Requirements